
How to Stop Phishing Emails Your Filter Missed (2026)
82% of phishing emails now use AI content. Configure Google and Microsoft admin settings, plus free tools that catch what built-in filters miss.
Cybersecurity and operational resilience insights for wealth management professionals. No jargon, no fear-mongering.

82% of phishing emails now use AI content. Configure Google and Microsoft admin settings, plus free tools that catch what built-in filters miss.
Your CRM holds your most valuable business data. If it's misconfigured, unmonitored, or running on spreadsheets, you're one mistake away from a real problem.

A single copy-paste prompt that researches your competitors, builds a professional website, and sets up free hosting on Cloudflare. No coding required.

A day-by-day walkthrough of the Solanasis Compliance Readiness Assessment, based on composite findings from typical wealth management firms. See what we check, what we find, and what you get.
Claude is brilliant but measures once and cuts twice. Here's how I set up Claude Code and Claude Cowork to verify findings through ChatGPT, and why the $20/month OpenAI subscription pays for itself.

Security assessments don't have to be scary. Here's what actually happens, what you'll get, and how to tell a useful assessment from a sales pitch.
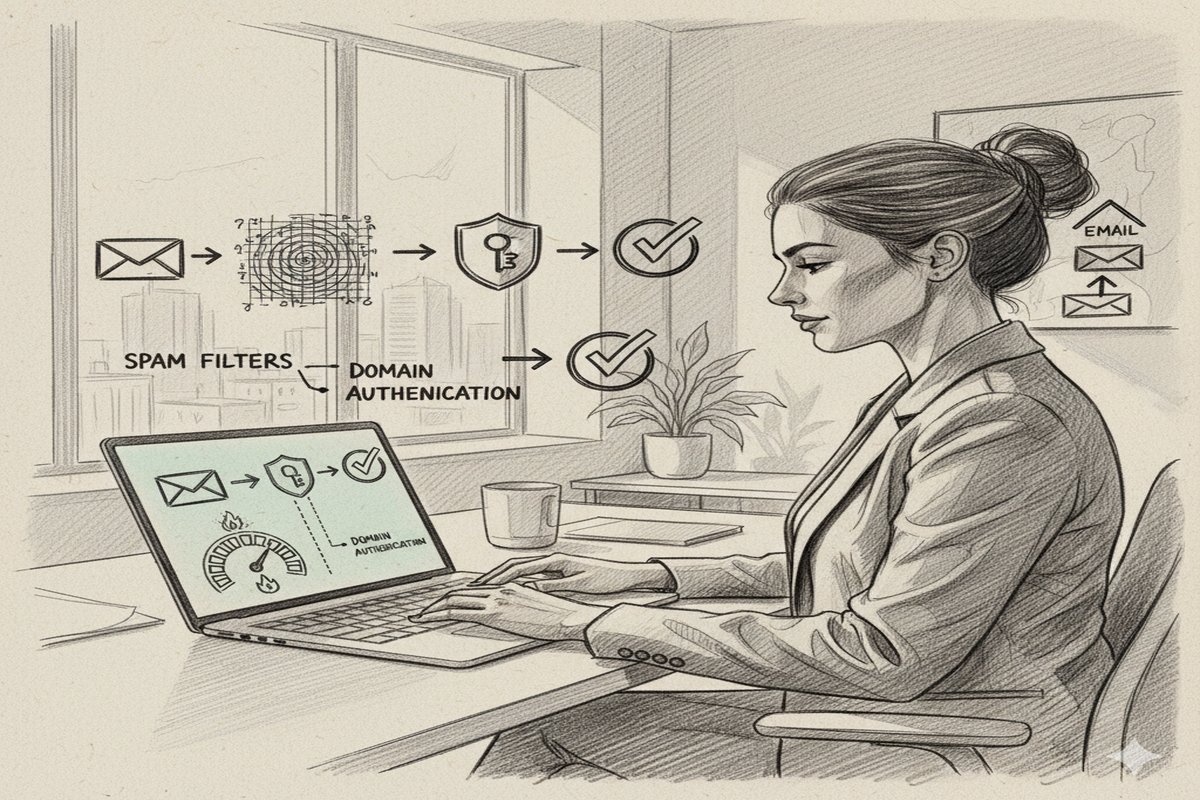
Most founders skip email warmup and wonder why their cold emails end up in spam. Here's the dual-layer warmup strategy using TrulyInbox and manual outreach that gets you into Primary inbox in 3-4 weeks.

LinkedIn has years of your professional data and they'll hand it over for free. Upload it to AI and the insights about your network, communication patterns, and career trajectory are surprisingly useful.

Most referral programs feel transactional. Ours is built for the people who actually put their reputation on the line: security consultants, managed service providers, and trusted IT advisors.

Most disaster recovery plans fail when they're needed most. Here's how to build one that holds up, starting with the question most teams skip.

Billions of passwords have been exposed in data breaches. Here's how to check yours for free, and what to do if you find a match.
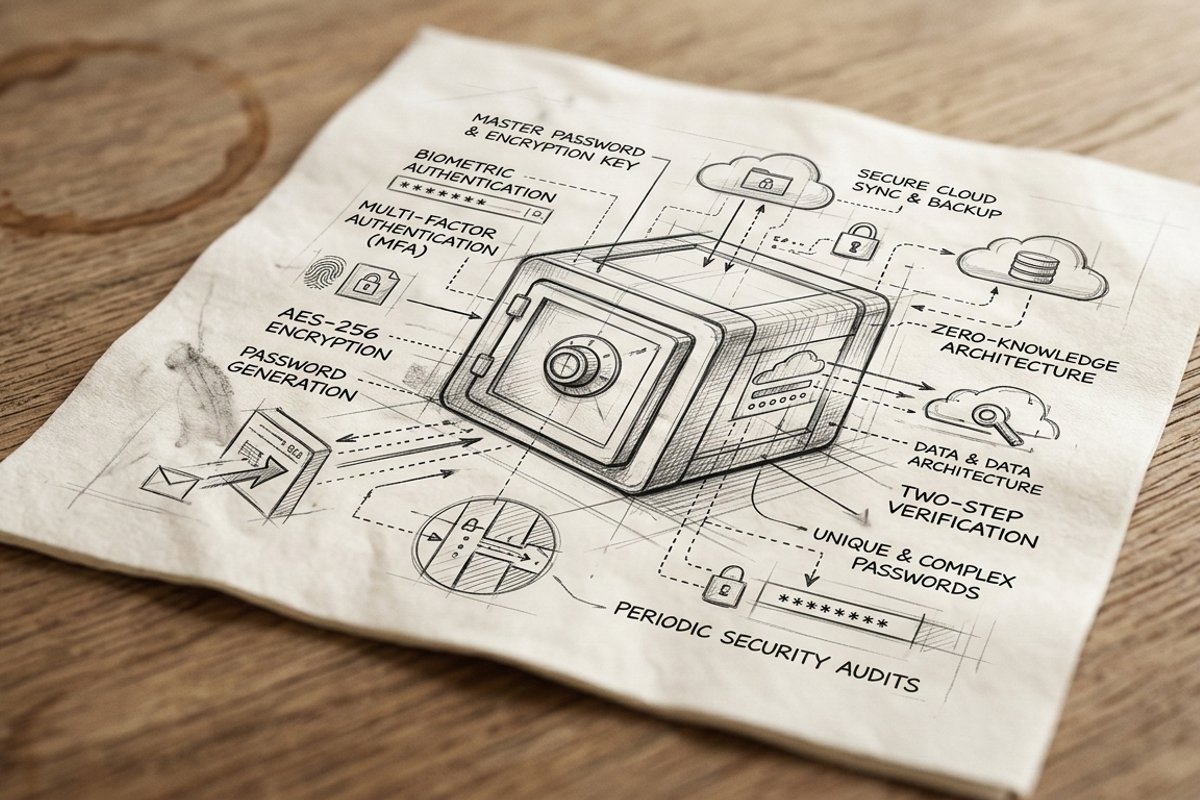
Shared passwords in spreadsheets and Slack messages are a security risk hiding in plain sight. Here's how to fix it in 30 minutes.